United States- DiscountMugs.comhttps://www.thepaypers.com/digital-identity-security-online-fraud/credit-card-data-breach-at-discountmugs-com/776755-26
Exploit: Injection of card skimming code into website.DiscountMugs.com: E-commerce website for custom mugs and apparel.
 | Risk to Small Business: 1.666 = Severe: When hackers can extract credit card numbers from your customers for four months long undetected, the aftermath is never good. Although the company identified that orders between August 5 and November 16 of 2018 had been compromised, the number of shoppers affected has not been determined. Customers will think twice before purchasing from the website and will likely consider competitors with better online security. |
 | Individual Risk: 2.428 = Severe: Given that the cyber attack occurred just before a busy holiday shopping season, you must wonder if the cyber criminals planned their timing strategically. They stole everything from credit card numbers, security codes, and expiration dates, to names, addresses, phone numbers, email addresses and ZIP codes. With this information in hand, anyone is capable of orchestrating payment fraud. |
Customers Impacted: To be determined.How it Could Affect Your Customers’ Business: Payment breaches are frightening for businesses and their customers. As American consumers begin to experience how cyber attacks affect them first-hand, they will put their digital dollars towards websites that can protect their financial information.ID Agent to the Rescue: Dark Web ID monitors the Dark Web and can help discover this form of breach before it hits the news cycle. We work with MSSPs to strengthen their security suite by offering industry-leading detection. Find out more here: https://www.idagent.com/dark-web/.
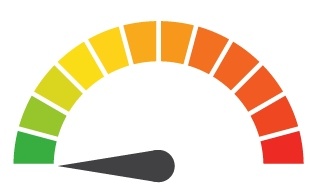
Risk Levels:1 - 1.5 = Extreme Risk1.51 - 2.49 = Severe Risk2.5 - 3 = Moderate Risk*The risk score is calculated using a formula that considers a wide range of factors related to the assessed breach.