Remember when you first got your smartphone and you were able to get
almost 48 hours out of one battery charge? Well, turns out that little
honeymoon phase doesn't last forever. The more use you get out of your
phone, the shorter its average battery life tends to get. A dead phone can
be an extreme inconvenience -- but it isn't a difficult thing to avoid. While
it will likely never last quite as long as it did in its glory days, here are
some helpful tips to extend your phone's battery life.
1. Figure out what's using
the most power
The first order of business is to find out what exactly is draining your
battery to begin with. Head on over to your phone's settings and look for the
"battery" section. There are a couple handy tools worth visiting
here. Most importantly, there will be a succinct breakdown of which apps or
services have been using most of your phone's battery power. Take note of the
top offenders -- what is it that's contributing most to your battery's
dwindling lifespan? The insight provided here can help you to be conscious of
the activities that are killing your battery so you can avoid them when
necessary.
2. Turn off functions that
aren't being used
One of the most common culprits when it comes to excessive battery usage
is having features on that aren't even being used. Functions such as WiFi, GPS
and Bluetooth can be pretty sneaky when it comes to draining your power. Try to
keep them off whenever possible. Turn Bluetooth off whenever you're done using
an external device. Keep WiFi and GPS off if you're at work, in class or
somewhere else you won't be frequently using your device (just make sure you
remember to switch your WiFi back on afterward so you don't use up your data).
Additionally, turn down your display brightness. Smartphone displays require
quite a bit of battery power, especially when their brightness is turned up.
You certainly don't have to keep it at the absolute minimum, but you'd be
surprised what your eyes can adjust to once you've gotten used to keeping your
display on a dimmer setting.
3. Persistently close apps
that are running in the background
A common misconception is that once an app is no longer on your
screen, it is no longer running. Unfortunately, this isn't the case. Leaving an
app through use of the home or back buttons usually pushes it into the
background rather than closing it. Think of this as minimizing a program
on your computer rather than exiting it entirely. These apps continue running
(and draining your battery life) until they're closed manually. Closing apps is
done differently on different devices, but try looking for a rectangle icon
next to your home button or double tapping the home button itself. Once you've
accessed the screen that shows all of your currently-running programs, simply
swipe them out of the way to close them. This is something that you should make
a habit of doing every time you lock your device.
4. Make sure your screen
always gets locked
Speaking of locking your device, it's important to make sure that you do
so. It's easy to drop your phone back into your pocket, purse, etc. without
remembering to lock the screen first. This means that your device is going to
stay lit up while it isn't being used, taking a huge toll on your battery life.
Additionally, you should adjust your display settings so that your phone screen
automatically dims just a short amount of time after being used. Navigate to
your device's settings and find the "display" section. In here,
you'll find a setting titled something along the lines of "screen
time-out" or "dim screen after 'x' number of seconds." Select
the shortest option available so that even if you put your device down without
remembering to lock it, the screen will still power down promptly and spare
your battery power.
5. Use a power bank
Lastly, an external power bank is an excellent investment if you have
issues with short battery life. Also referred to as "external
batteries" or "portable chargers," power banks allow you to
charge your device on the go as long as they've got some juice in them. A lot
of people don't necessarily think that they need a power bank, but you might be
surprised just how much use you'll get out of it. You can even find highly
rated ones at pretty low prices if you browse Amazon. At the end of the day
when you charge your device, make a habit of plugging in a power bank as well.
This way, your device can essentially have a second life once its internal
battery gets low.
Having a phone that dies halfway through the day can be both stressful
and inconvenient. Fear not -- taking these tips into account is sure to extend
its battery life.
More questions? Contact me at 877.860.5831 x190
Robert Blake

 suddenly all over the news. In hindsight, it was a matter of "not if, but when".
suddenly all over the news. In hindsight, it was a matter of "not if, but when". 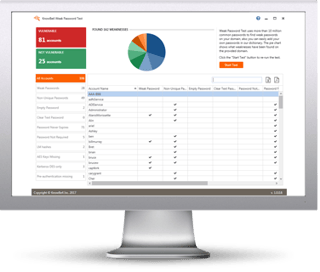 How weak are your user's passwords? Are they... P@ssw0rd?
How weak are your user's passwords? Are they... P@ssw0rd?





