If cybersecurity jargon like SOC, MDR, and zero-trust overwhelms you, you're not alone. Most business leaders need clarity and peace of mind, not technical terminology. Understanding the tools is just the first step.The real question is: How do you build a cybersecurity fortress that actually works for your business?That's why I'm personally inviting you to join us for an executive briefing:
The 2026 Cyber Threat Landscape: A Leader's Guide to Business ResilienceDate & Time: April 7th at 11:00 AM ET
- The critical gap between owning security tools and having true security operations
- What 24/7 monitoring and incident response actually look like in practice
- How to build a security strategy that delivers confidence, compliance, and peace of mind
This isn't a technical deep dive. It's a strategic conversation designed specifically for business leaders like you.Want a sneak peak? We've just published a new article that cuts through the noise:"SOC & MDR Explained (In Plain English): Your 24/7 Cybersecurity Answer."It breaks down exactly what a Security Operations Center and Managed Detection and Response mean for your business, and why they matter.
Best regards,Ivan Shore
VP of Sales and Marketing
Bit by Bit
Technology companies come and go, but Bit by Bit backs its service with 30 years of experience helping businesses achieve their goals with reliable IT solutions and support. We were established in 1987 as a database application development and networking company, and since then we’ve evolved into a full-service IT firm and leader in delivering powerful and cost-effective technology solutions. visit our site at www.bitxbit.com
Tuesday, March 24, 2026
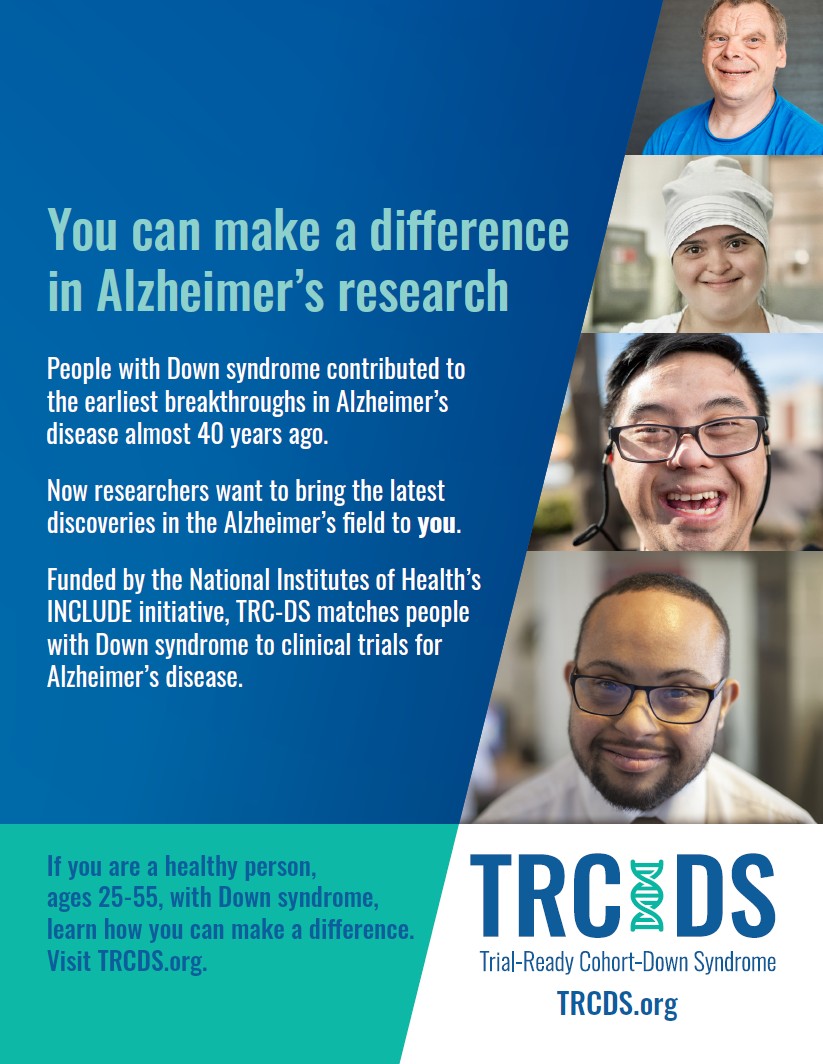
Trial-Ready Cohort-Down Syndrome Study Info
Trial-Ready Cohort-Down Syndrome Study
As mentioned, the TRC-DS study stands for Trial-Ready Cohort-Down Syndrome.
- It is an observational study looking for healthy adults between the ages of 25 and 55 with Down syndrome to participate and become part of a larger movement advancing Alzheimer's disease therapies and potential cures for people with Down syndrome.
- It is a 4 year (48 month) study where you will be required to come in about 8 times.
- The first visit will last about 4-5 hours
- The MRI will be done on a separate day.
- Study procedures include cognitive testing, MRI, blood draw, and a visit with a neurologist.
Below are links to three flyers with information.Tania Romero, BSPHClinical Research Coordinator I- NeurologyCognition and MemoryUT Southwestern5303 Harry Hines Blvd. 9th Floor, Dallas, TX 75390-8869Office: 214-648-9331Text: 214-620-0377
It's not too late!
Arlington, TX 76012Email not displaying correctly?
Friday, March 20, 2026
AI Without Control: The Real Risk to Your Business Data
AI Without Control: The Real Risk to Your Business Data
Artificial Intelligence is no longer a future concept—it’s already embedded in how businesses operate.
Employees are using tools like ChatGPT, Claude, and Microsoft Copilot to draft emails, analyze documents, and improve productivity.
But while adoption is accelerating, one critical issue is often overlooked:
AI is being used faster than it is being governed.
The Wrong Question: “Which AI Is Safe?”
Many organizations start here:
“Which AI platform is the most secure?”
It sounds reasonable—but it misses the bigger point.
No AI platform is automatically “safe” on its own.
Security depends on how the tool is configured, deployed, and governed within your organization.
The same platform can either:
Enhance productivity securely
Or introduce serious data exposure
The difference is not the tool—it’s the controls around it.
Understanding the Real Risk: Uncontrolled AI Usage
In many organizations, AI adoption begins informally:
Employees testing tools on their own
Using personal accounts for business tasks
Sharing documents with AI platforms without oversight
This creates several risks:
Sensitive data leaving your environment
No visibility into what was shared
No audit trail or accountability
This is often referred to as “Shadow AI”—and it’s becoming one of the fastest-growing security concerns in modern workplaces.
Why Evaluation Must Come First
Before adopting any AI platform, organizations need a structured evaluation process.
Not after deployment—before it.
Key areas to evaluate:
1. Data Usage and Privacy
Understand:
Is your data used to train the model?
Where is it stored?
How long is it retained?
Enterprise offerings—such as ChatGPT Enterprise or enterprise deployments of Claude—typically provide stronger data controls than consumer or unmanaged versions.
However, consumer and enterprise versions often have very different data handling policies and must be evaluated separately.
2. Access Control and Identity Management
Secure deployments should include:
Single Sign-On (SSO)
Role-based access controls
Centralized user management
Without this, AI becomes another unmanaged entry point into your environment.
3. Compliance and Regulatory Alignment
AI usage must align with your organization’s obligations, including:
Data privacy requirements
Industry regulations
Internal governance policies
It’s important to note:
AI platforms may support compliance—but they do not automatically make your organization compliant.
Configuration, usage policies, and oversight still matter.
4. Monitoring and Auditability
Organizations should be able to answer:
Who used the AI?
What data was entered?
What output was generated?
Without visibility, there is no accountability—and no way to manage risk.
There Is No One-Size-Fits-All AI Strategy
Different AI platforms excel in different areas:
Claude is often strong in document analysis and structured reasoning
Microsoft Copilot integrates deeply with Microsoft environments
ChatGPT offers flexibility across a wide range of use cases
Rather than selecting a single tool, many organizations are adopting a use-case-driven approach, aligning the right AI solution to the right business need.
Building a Controlled AI Framework
To safely adopt AI, organizations should establish clear governance from the start.
A strong framework includes:
Approved Platforms
Limit usage to vetted, enterprise-grade tools
Defined Data Policies
Clarify what data can and cannot be used with AI
Centralized Access
Require managed accounts and eliminate personal usage for business purposes
Usage Monitoring
Maintain visibility into how AI tools are being used
Human Oversight
Ensure outputs are reviewed before business decisions are made
AI Is a Business Risk Decision—Not Just an IT Decision
AI impacts:
Sensitive business data
Customer information
Internal operations
This makes it more than a technology initiative.
It is a governance, risk, and compliance decision.
Organizations that move forward without structure may gain short-term efficiency—but increase long-term exposure.
Those that implement AI with clear controls can:
Improve productivity
Protect data integrity
Maintain compliance
Build a sustainable advantage
Final Thought: Control Before Scale
AI is not something to avoid—it’s something to manage correctly.
Before expanding AI across your organization, ask:
Do we have clear control over how AI is being used today?
If the answer is unclear, the next step isn’t expansion—it’s evaluation.
At Bit by Bit Computer Consulting, we help organizations adopt AI securely—balancing innovation with control, compliance, and real-world business needs.
If you’re evaluating tools like ChatGPT, Claude, or Microsoft Copilot and want to ensure your business is protected from unintended risk:
🌐 www.bitxbit.com
📞 877.860.5831
Let’s build an AI strategy that works—securely, responsibly, and with confidence.
Monday, March 16, 2026
“An Account Was Created for You” — Should You Trust It?
“An Account Was Created for You” — Should You Trust It?
Cybersecurity threats have changed.
Today’s phishing emails don’t look sloppy or suspicious. They look professional, familiar, and urgent—often referencing real companies and real services.
One of the fastest-growing tactics we’re seeing is the “Account Created for You” email.
How This Scam Works
The email claims that:
An account has been created for you
A trusted company or partner initiated it
You need to log in, verify, or delete the account
These messages are designed to trigger confusion and urgency. The goal is simple: get you to click before you think.
Once clicked, the link may:
Capture your login credentials
Redirect you to a fake sign-in page
Install malicious software
Grant attackers long-term access to your email or systems
Common Red Flags to Watch For
If you see any of the following, stop and verify before acting:
You did not request the account
The email references an unfamiliar event, meeting, or system
The message pressures you to act immediately
There are misspellings or awkward phrasing
The sender address looks automated or generic
The email asks you to “delete” or “secure” an account via a link
Modern phishing relies on plausibility, not obvious mistakes.
What You Should Do Instead
If you receive an unexpected account creation email:
Do not click any links in the message
Open a browser and go directly to the company’s website
Use the official “Forgot Password” option to check if an account exists
Report the email as phishing to your IT team or email provider
If this is a business email, notify IT immediately
This simple pause can prevent account compromise.
Why This Matters for Businesses
For organizations, a single compromised email account can lead to:
Internal phishing attacks
Data exposure
Unauthorized system access
Financial fraud
Regulatory and compliance risks
Security incidents don’t always start with malware.
Often, they start with one believable email.
The Bottom Line
If an email surprises you, pressures you, or asks you to act fast—
that’s your cue to slow down.
Modern phishing doesn’t look fake.
It looks familiar.
Need Help Protecting Your Organization?
If you’d like help with:
Phishing awareness training
Email security controls
Account monitoring and response
Security best practices for your business
Bit by Bit Computer Consulting is here to help.
Visit www.bitxbit.com or call 877-860-5831 to learn more.
Monday, March 2, 2026
Scam Alert: A Fake McAfee Invoice Is Making the Rounds — Here’s How to Spot It (and What to Do If You Fall for It)
Recently, we saw a fake invoice email pretending to be from McAfee that was sent to over 140 random recipients at once—across AT&T, Yahoo, Gmail, iCloud, and other providers.
At first glance, it looks official. Logos. Invoice numbers. A dollar amount. Even a “helpdesk” phone number.
But this message is 100% fraudulent.
Let’s break down the easy-to-spot red flags, what you should never do, and exactly what to do if you already interacted with it.
🚩 The Easy Red Flags (Using This Email as the Example)
1. It Was Sent to Dozens (or Hundreds) of Random People
Legitimate companies do not send invoices using mass distribution lists.
If you see:
Many unrelated email addresses in To, CC, or BCC
Addresses across different providers (AT&T, Gmail, Yahoo, iCloud)
👉 That alone is enough to treat it as a scam.
2. Generic Greeting: “Hi there, Client.”
Real invoices use:
Your full name, or
Your company name, or
At least the email tied to the account
Scammers avoid specifics because they don’t know who you are.
3. Urgent Language About Charges You “Didn’t Approve”
This line is classic social engineering:
“If you did not give authorization for this transaction, please contact us…”
They want you to panic first and think later.
Legitimate vendors don’t resolve billing disputes by pushing you to call immediately.
4. The Phone Number Is the Trap
This is the most important part:
The entire scam depends on you calling the number
Once you call, they:
Ask for remote access
Request payment details
Or “refund” money using fake banking screens
⚠️ Never call phone numbers listed in unsolicited invoices. Ever.
5. The Amount Is “High Enough to Hurt, Low Enough to Believe”
$375.98 is intentional:
Not outrageous
Not trivial
Just enough to make people react
This is a known scammer pricing tactic.
6. Fake Renewal Terms That Don’t Make Sense
“Automatically renewed for a further three years, lasting 24 hours.”
That sentence alone is nonsense—and a strong sign it was written overseas or stitched together from templates.
7. The Sender Address Doesn’t Match the Brand
Even if the logo says “McAfee,” the email came from:
An unrelated domain
Or a compromised personal/business account
Brand logo ≠ brand sender
❌ What You Should NOT Do
If you receive an email like this:
❌ Do not call the phone number
❌ Do not reply to the email
❌ Do not click links or open attachments
❌ Do not trust the invoice just because it looks professional
✅ What You SHOULD Do Instead
Step 1: Assume It’s Fake
Even if you do use the product mentioned, assume fraud until proven otherwise.
Step 2: Check Accounts the Safe Way
If you’re concerned:
Open a new browser window
Go directly to the company’s official website
Log in from there (not via email links)
Step 3: Report and Delete
Mark the email as Spam / Phishing
Delete it
Move on
That helps your email provider protect others.
😬 What If You Already Fell for It?
Don’t panic—this happens to smart people every day.
If You Called the Number:
Hang up immediately
Do not continue the conversation
If You Gave Payment Information:
Call your bank or credit card company right away
Request:
A charge reversal (if applicable)
A card replacement
Fraud monitoring
If You Installed Remote Access Software:
Disconnect from the internet
Power off the computer
Have a professional check and clean the system
Change passwords from a different device
Why These Scams Work (and Why They’re Increasing)
Scammers succeed because they:
Use real brand names
Mimic legitimate invoices
Rely on urgency and fear
Target people outside of IT departments
This is exactly why security awareness matters just as much as antivirus software.
Final Thought
If an email pressures you to act immediately, financially, and outside normal processes, slow down.
Scams thrive on speed.
Security starts with pause and verification.
If you’d like help educating your team, clients, or family members on real-world phishing and invoice fraud, that’s exactly the kind of awareness that prevents costly mistakes.
Monday, February 16, 2026
Cyber Insurance Is Getting Stricter in Texas — and IT Decisions Now Determine Coverage
For years, many Texas businesses viewed cyber insurance as a simple checkbox: fill out an application, pay the premium, and assume coverage would be there if something went wrong. That era is over.
Today, Texas cyber insurers are tightening requirements, limiting coverage, and outright denying claims when companies fail to maintain basic security controls. The result? Your IT decisions now directly impact not just security—but whether you’re insurable at all.
What Texas Cyber Insurers Are Now Requiring
Across Texas, insurers are increasingly mandating proof of specific controls before issuing or renewing policies. Common requirements include:
Multi-Factor Authentication (MFA)
Required for email, remote access, and administrative accounts. Passwords alone are no longer acceptable.Endpoint Detection & Response (EDR / XDR)
Traditional antivirus is considered insufficient. Insurers want active threat detection and response capabilities.Regular Patching & Updates
Operating systems, applications, and network devices must be patched consistently and documented.Backup & Disaster Recovery
Backups must be secure, tested, and isolated—especially from ransomware attacks.Security Awareness Training
Employees must receive ongoing training to reduce phishing and social engineering risk.
These controls are no longer “best practices.” In Texas, they are quickly becoming minimum standards.
Why Claims Are Being Denied
One of the most alarming trends is post-incident claim denial.
After a breach or ransomware event, insurers are scrutinizing whether the insured organization actually maintained the controls they claimed. If gaps are found, claims are often rejected under language citing:
“Failure to maintain reasonable security controls.”
In many cases, companies believed they were covered—until they weren’t.
Why This Matters for Texas Businesses
Texas continues to be a prime target for cyberattacks due to its concentration of:
Engineering and construction firms
Manufacturing and energy companies
Healthcare and professional services
Mid-sized organizations with limited internal IT resources
At the same time, cyber insurance premiums are rising, coverage limits are shrinking, and underwriting questionnaires are becoming more technical.
IT is no longer just an operational concern—it’s a financial and risk-management issue.
The MSP Advantage: Turning Insurance Requirements into Strength
A Managed Service Provider (MSP) helps Texas businesses move from reactive IT to defensible, insurable security posture by:
Implementing and monitoring required security controls
Maintaining documentation insurers expect to see
Ensuring backups and recovery plans are tested, not assumed
Keeping systems patched and compliant year-round
Providing ongoing employee security training
This doesn’t just reduce cyber risk—it improves your position with insurers, brokers, and auditors.
Final Takeaway
Cyber insurance in Texas is no longer forgiving. If your IT environment doesn’t meet modern security standards, you may:
Pay higher premiums
Face reduced coverage
Have claims denied when you need them most
The right IT strategy—and the right MSP—can mean the difference between a covered incident and a costly business failure.
Monday, February 2, 2026
Why Engineering Firms Should Rely on a Managed Service Provider for IT & Security
Engineering companies operate in a high-stakes environment. Your designs, calculations, and intellectual property are mission-critical—and downtime, data loss, or security failures can halt projects, delay deliverables, and damage client trust. As technology becomes more complex and cyber threats more targeted, many engineering firms are finding that relying on a Managed Service Provider (MSP) is no longer optional—it’s a strategic advantage.
Below is why partnering with an MSP makes sense for modern engineering organizations.
1. Engineering Workloads Demand Specialized IT Support
Engineering firms rely on demanding systems:
CAD and BIM platforms
Simulation and modeling software
Large file storage and secure file sharing
High-performance workstations and servers
An MSP understands how to design, maintain, and optimize infrastructure for these workloads—ensuring your engineers spend time engineering, not troubleshooting technology.
2. Cybersecurity Threats Target Engineering Firms
Engineering firms are prime targets for cybercriminals due to:
Valuable intellectual property
Infrastructure and utility project data
Government and defense-related contracts
A qualified MSP provides layered security, including:
Endpoint detection and response (EDR)
Firewall and network monitoring
Email security and phishing protection
Security awareness training for staff
Backup and ransomware recovery planning
This proactive approach dramatically reduces risk compared to reactive, break-fix IT.
3. Compliance Is Increasingly Complex
Depending on your clients and projects, engineering firms may need to address:
Client-mandated cybersecurity standards
Cyber insurance requirements
Data privacy regulations
Vendor security assessments
An MSP helps document, implement, and maintain controls—reducing exposure and making audits and questionnaires far less painful.
4. Predictable Costs Instead of Costly Surprises
Hiring and retaining in-house IT talent is expensive—and a single person can’t cover everything from cybersecurity to cloud strategy.
With a managed services model, you get:
Predictable monthly costs
Access to an entire team of specialists
24×7 monitoring and support
Scalable services as your firm grows or contracts
This model aligns IT spending with business outcomes rather than emergency repairs.
5. Business Continuity for Projects and Deadlines
Engineering timelines are unforgiving. System outages, data corruption, or ransomware can derail weeks—or months—of work.
An MSP ensures:
Regular, tested backups
Disaster recovery planning
Redundant systems where appropriate
Fast response when issues arise
That resilience keeps projects moving and clients confident.
6. Strategic IT Guidance, Not Just Helpdesk Support
The right MSP doesn’t just “fix things”—they act as a technology partner, helping engineering firms:
Plan hardware refresh cycles
Migrate to secure cloud platforms
Support remote and hybrid teams
Improve performance of design applications
Align IT strategy with long-term business goals
This turns IT from a cost center into a competitive advantage.
Final Thought: Engineers Should Engineer—Let Experts Handle IT
Your engineers are hired for their technical expertise, creativity, and problem-solving—not to manage firewalls, patch systems, or recover from cyber incidents.
A trusted Managed Service Provider allows your firm to:
Reduce risk
Improve reliability
Control costs
Focus on delivering high-quality engineering work
Ready to Strengthen Your IT and Security?
Bit by Bit Computer Consulting works with engineering firms to provide secure, reliable, and scalable IT solutions—from daily support to advanced cybersecurity and compliance guidance.
📞 Call: 877.860.5831
🌐 Visit: www.bitxbit.com
Let’s make sure your technology supports your engineering—not the other way around.
Subscribe to:
Posts (Atom)
-
Windows 10 End-of-Life: Why You Must Upgrade Now to Stay Secure and Compliant Microsoft has officially announced the end of support for Win...
-
What is SOC-as-a-Service? By Robert Blake Having a Security Operations Center (SOC) in-house is expensive for the average business. Large ...
-
In today’s digital-first world, non-profit organizations are under increasing pressure to secure sensitive data, streamline operations, and ...