United Kingdom - Steelite
Exploit: Ransomware.
Steelite: A Middleport-based company that manufactures tableware for the hospitality industry.
Steelite: A Middleport-based company that manufactures tableware for the hospitality industry.
 | Risk to Small Business: 1.888= Severe: The risk to small business in this scenario is very high. Ransomware is becoming more and more prevalent in the cyber-crime scene as it is a low-risk/ high reward attack vector. |
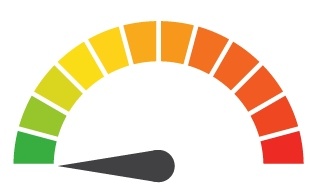 | Individual Risk: 2.571= Moderate: It is unclear if payroll information was accessed, but due to the sensitive nature of the encrypted files, it would be best to be cautious. |
How it Could Affect Your Customers’ Business: Payroll information is vital for operating a business, which makes this attack particularly damaging. Many organizations would not have the resources available to rebuild their payroll servers so quickly, which would leave them in a precarious situation.
ID Agent to the Rescue: ID Agent offers Dark Web ID™ which discovers compromised credentials that could be used to implement a crypto jacking script. Make sure your credentials are safe; for more information go to https://www.idagent.com/dark-web/.
Risk Levels:1 - 1.5 = Extreme Risk1.51 - 2.49 = Severe Risk2.5 - 3 = Moderate Risk*The risk score is calculated using a formula that takes into account a wide range of factors related to the assessed breach.



